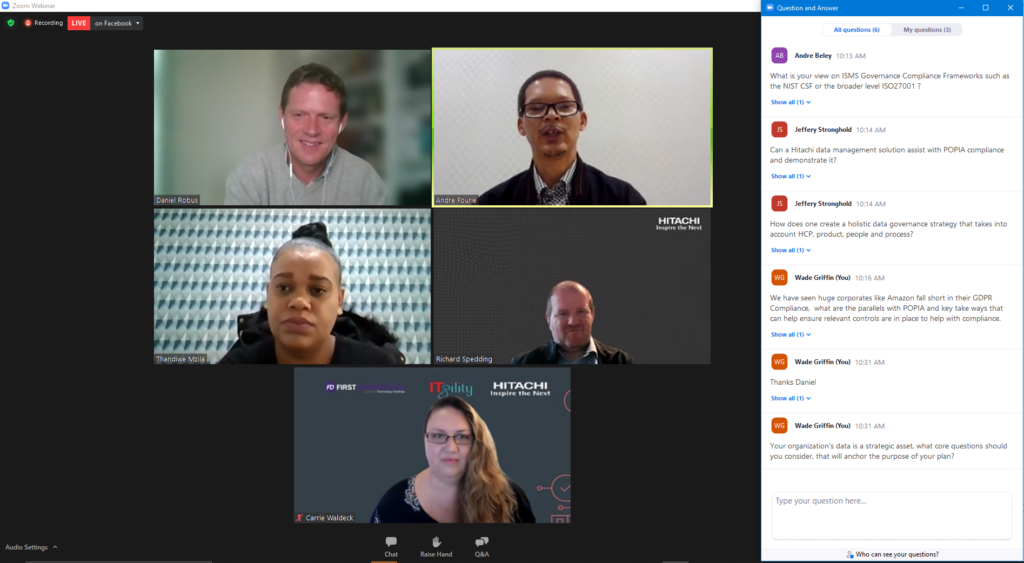
In the ITgility Hitachi webinar, experts discuss how funds can ensure adequate data protection as data sets grow, and data is created and consumed in distributed locations.
Cybercriminals are continuously finding ways to circumvent corporate security to gain access to sensitive data, despite increased emphasis being placed on data security. As a result, US$11.4 million a minute is being lost due to cybercrime according to the World Economic Forum Global Risks Report 2020.
A number of aspects put information at risk, including human error, infrastructure failure, targeted attacks like malware and ransomware attacks, and natural disasters, which can also lead to data deletion or corruption.
A breach can significantly impact a company and the repercussions of not properly protecting your data include lost opportunities, stiff fines and penalties, major business disruptions, or even, in extreme cases, loss of life.
As a result, data backup, recovery, and protection solutions are vital, and increasingly account for large amounts of IT budget. Globally, $43 billion is spent on data storage a year, $207 billion on data centres, and $7 billion just on information archiving.
Data intelligence technical expert at Hitachi Vantara, Richard Spedding, explains that the biggest problem with cyberattacks is they come from organised crime syndicates, not just a lone hacker sitting in his darkened bedroom. As a result, he says, they will become part of day-to-day IT management, and increasingly consume time at C-suite level because this is an issue for the entire organisation.
This issue is not limited to developed countries, it’s a problem that Hitachi Vantara is experiencing across its markets. According to Richard, ransomware ranks in the top five of security threats faced by its customers, regardless of where they are in the world.
Protecting data
Andre Fourie, director of operations at ITgility says that to counter such threats, companies require multiple layers of security just to make it a little bit more challenging for the intruders. “You also want to keep an eye on your system logs, to see if there are any anomalies in your environment.”
Andre recommends investing in security information and event management, which captures event data from a variety of sources across the organisation throughout the entire network. It logs an inflow of data from end-users, applications, assets, cloud environments and so on, which can be analysed in real-time. “If there’s something abnormal happening in your environment, you will be able to pick it up and hopefully do something about it before you suffer a ransomware incident.”
Repeated failed logins, for example, could be a criminal trying to brute force their way into a system, notes Andre. A security information and event management system can also pick up malware before it spreads. However, he says, companies have to either automate processes to respond to alerts, or act quickly when they are picked up.
Richard adds that a good framework is important, and companies need to implement this themselves as government regulation does not require a system to be installed.
You also have to consider that information doesn’t just exist in the data centre anymore, it’s also on mobile phones and laptops, says Fourie. “You can have a good security posture within your data centre, but if you don’t protect your endpoint devices, your sensitive data might be out there.”
This requires encryption so that if anything happens to the device, the data is still secure. “Twenty-eight percent of today’s data is sitting outside the data centre and only 72% sits in the data centre,” he emphasises.
Thandiwe Mzila, director of marketing at ITgility, notes that customers tend to focus on two aspects: backup and replication. There are pros and cons to each type of backup, which tends to take the form of either disk to tape or disk to disk. Regardless of the backup type, restoring an operation following a data breach can take up to a day, she says.
At the same time, says Thandiwe, very few companies are replicating data. Fourie adds that data, backup, and recovery are subsets of data protection.
What the law requires
In terms of legislation, be it the European General Data Protection Regulation or South Africa’s Protection of Personal Information Act, Richard says businesses need to ensure they protect data they own, hold and store.
Andre adds that, in terms of data governance, companies need to take control of their information including knowing where it is located, the source of data, its classification, who has access, as well as its contents.
The first step, Andre advises, is to conduct a data inventory and audit what data you have, who is accessing it.
Richard explains that companies need to be selective about the data they keep, and to classify their data. Because much data is unstructured, or semi-structured, this process needs to be automated. Artificial intelligence, or machine learning, can be used to develop a fingerprint of what data looks like and classify and process it accordingly. The machine needs to be taught first, he adds.
Thandiwe points out that, at the end of the day, the key to data governance is security. “Speed and access to data, as well as mandatory compliance requirements, introduce a huge amount of cost. This is a critical aspect the organisation needs to consider, when looking at compliance and how to gather data and ensure that it’s secure.”
ABOUT THE SPEAKERS
THANDIWE MZILA
Director of Marketing @ ITgility
Thandiwe Mzila one of the directors at ITgility and has been part of the team since 2011. Thandi has been part of the ICT industry since 2007. After graduating from North-West University Thandi joined the IBM graduate programme as part of the mainframe team. Thandi joined ITgility in year 2011 as a junior manager responsible for client relationships. In 2017 Thandi managed to become part of the executive team responsible for marketing.
ANDRE FOURIE
Director of Operations @ ITgility
Andre Fourie is one of the co-founders of ITgility and has been part of the team since 2011. Andre has been part of the ICT industry since 1990 and has performed in various roles. At ITgility, Andre is part of the consulting team (virtualisation, data management, backup solutions, cloud offerings), including managing operational responsibilities.
Andre has extensive experience in enterprise accounts as well as small and medium businesses delivering various solutions.
RICHARD SPEDDING
Data Intelligence Technical Expert @ Hitachi Vantara
Richard Spedding has worked at Hitachi Vantara for the last 13 years as a technical expert, focusing on data management and data intelligence. Richard works with customers to deliver solutions at global scale, solving customer problems around compliance, governance, data consolidation, analytics, ai, and machine learning, allowing customers to unlock valuable insight from their data, whilst maintaining a well-governed data infrastructure.
Richard has worked in the Storage industry for over 30 years and has maintained a focus on data longevity and lifecycle management. Richard has worked in storage distribution, as well as with Legato & EMC Corporation.